Securing IoT P2P Connections With SSH: A Comprehensive Guide
In today's highly interconnected world, establishing secure peer-to-peer SSH connections for IoT devices is no longer optional—it's essential. With billions of devices now connected to the internet, ensuring secure communication between them is critical for safeguarding sensitive data and preserving privacy. As technology continues to evolve, the demand for robust security solutions, particularly in the realm of peer-to-peer (P2P) SSH connections for IoT devices, has never been higher.
The rapid expansion of the Internet of Things (IoT) has ushered in a new era of innovation and convenience. However, it has also introduced significant security challenges. Devices that were once isolated are now part of expansive networks, making them vulnerable to unauthorized access and cyberattacks. Understanding how to securely establish remote IoT P2P SSH connections is therefore vital for both individuals and businesses.
This article will explore the concept of secure IoT P2P SSH connections in depth. We'll examine the free tools and solutions available, as well as provide actionable tips to enhance your network security. Whether you're a tech enthusiast, a small business owner, or an enterprise IT manager, this guide will equip you with the knowledge and tools you need to protect your IoT ecosystem effectively.
Read also:Exploring Movierulz 7 A Comprehensive Guide For Movie Enthusiasts
Table of Contents
- Introduction to IoT P2P SSH
- Why Securing Remote IoT P2P SSH Connections Matters
- Understanding the Basics of SSH and IoT
- Free Tools for Securing IoT P2P SSH Connections
- Setting Up Secure Connections
- Best Practices for IoT Security
- Common Challenges in IoT Security
- The Future of IoT and P2P SSH
- Comparing Popular SSH Tools
- Conclusion
Introduction to IoT P2P SSH
IoT P2P SSH refers to the secure communication process between IoT devices using the Secure Shell (SSH) protocol. SSH is a cryptographic network protocol designed to provide secure data communication, remote command execution, and other secure network services. By leveraging SSH, IoT devices can communicate directly with one another in a peer-to-peer manner, eliminating the need for centralized servers and significantly reducing latency.
What is IoT?
The Internet of Things (IoT) is a network of interconnected physical devices, vehicles, appliances, and other objects embedded with sensors, software, and connectivity capabilities. These devices can exchange data seamlessly, enabling smarter and more efficient systems. From simple household gadgets to sophisticated industrial machinery, IoT devices are transforming the way we interact with technology.
Why Use SSH for IoT?
- Encryption: SSH encrypts all data transmitted between devices, ensuring that sensitive information remains confidential.
- Authentication: It provides robust authentication mechanisms, verifying the identity of devices to prevent unauthorized access.
- Integrity: SSH ensures data integrity by detecting any unauthorized modifications during transmission, safeguarding the reliability of the communication.
Why Securing Remote IoT P2P SSH Connections Matters
As the number of IoT devices continues to grow exponentially, so does the risk of cyber threats. Without proper security measures, these devices can become easy targets for hackers, leading to data breaches, financial losses, and even physical harm. Securing remote IoT P2P SSH connections is essential for protecting sensitive information and maintaining the integrity of your network.
Consequences of Insecure IoT Connections
- Data Theft: Unauthorized access to sensitive data can lead to privacy violations and financial losses.
- Unauthorized Access: Hackers can exploit vulnerabilities to gain access to critical systems, compromising security.
- Service Disruption: Cyberattacks can disrupt services and operations, causing significant downtime and inconvenience.
Understanding the Basics of SSH and IoT
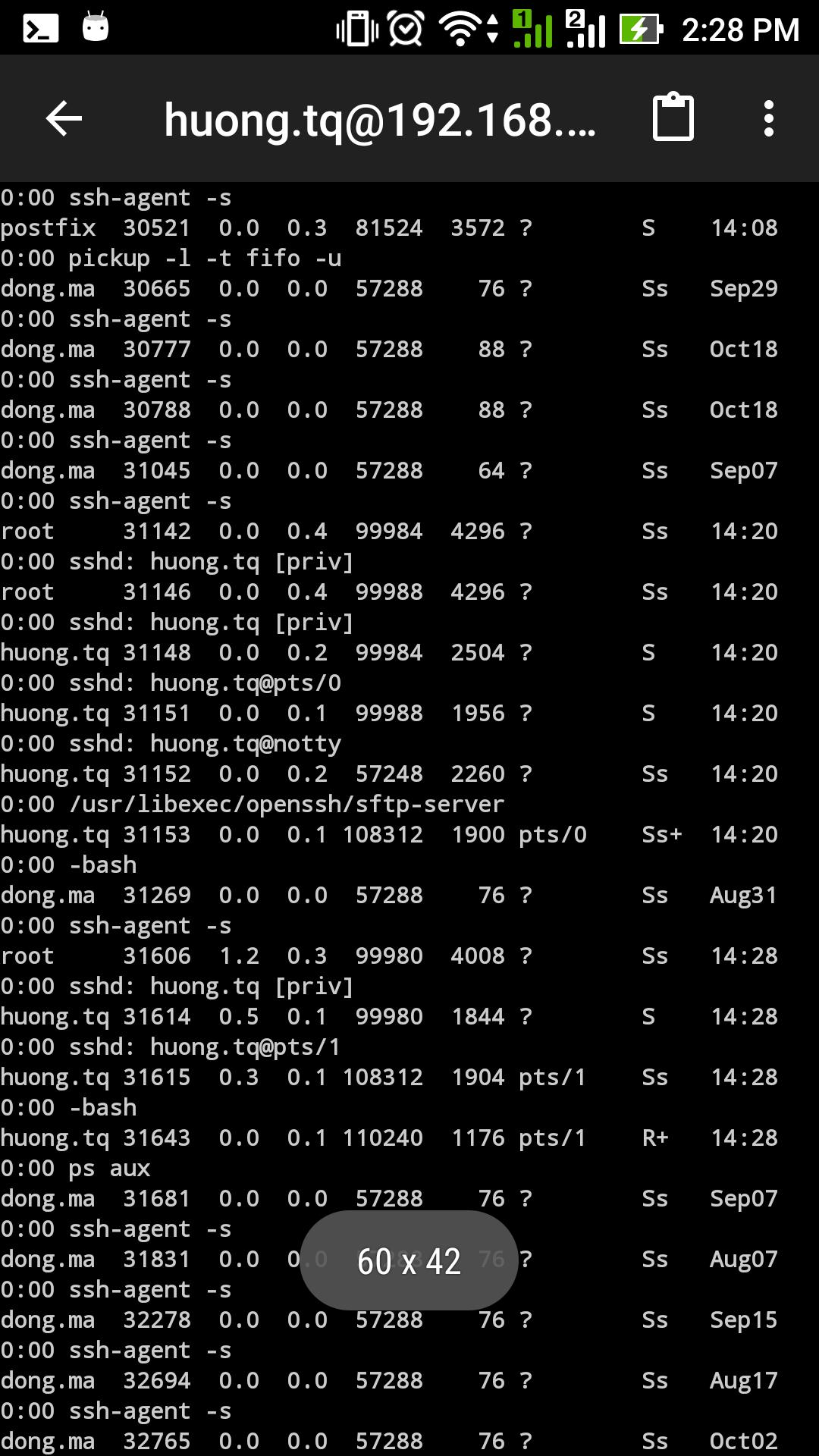
To fully grasp the concept of securing remote IoT P2P SSH connections, it's important to understand the fundamentals of SSH and its role in IoT security. SSH operates on a client-server model, where a client initiates a connection to a server. In the context of IoT, devices can act as both clients and servers, enabling seamless peer-to-peer communication.
Key Components of SSH
- Public Key Infrastructure (PKI): This is used for secure authentication, ensuring that only authorized devices can communicate with each other.
- Encryption Algorithms: Advanced encryption algorithms like AES and RSA ensure data confidentiality, protecting it from interception and unauthorized access.
- Port Forwarding: This feature allows secure access to services running on remote devices, enhancing the functionality of IoT networks.
Free Tools for Securing IoT P2P SSH Connections
Luckily, there are several free tools available that can help you establish secure IoT P2P SSH connections. These tools are designed to be user-friendly while maintaining robust security features. Below are some of the most popular options:
1. OpenSSH
OpenSSH is an open-source implementation of the SSH protocol. It is widely supported across various platforms, making it an excellent choice for securing IoT P2P SSH connections. OpenSSH offers strong encryption, authentication, and key management capabilities, ensuring the highest level of security for your devices.
Read also:Exploring Movierulzla Kannada Risks Legal Concerns And Alternatives
2. Dropbear
Dropbear is a lightweight SSH server and client, ideal for resource-constrained IoT devices. It supports most SSH features and is easy to configure, making it a popular choice for embedded systems. Its minimal footprint ensures that even devices with limited processing power can benefit from secure communication.
Setting Up Secure Connections
Setting up secure IoT P2P SSH connections involves several steps, from configuring your devices to establishing trusted connections. Below is a step-by-step guide to help you get started:
Step 1: Install SSH Client and Server
Begin by installing an SSH client and server on your devices. For Linux-based systems, you can use the following command:
sudo apt-get install openssh-server
Step 2: Generate SSH Keys
Create SSH keys to enable secure authentication. Use the following command:
ssh-keygen -t rsa -b 4096
Step 3: Configure Firewall Settings
Ensure your firewall allows SSH traffic on the appropriate ports (default is 22). Adjust your firewall rules accordingly:
sudo ufw allow 22
Best Practices for IoT Security
While securing remote IoT P2P SSH connections is crucial, it's just one part of comprehensive IoT security. Below are some best practices to further enhance the security of your IoT ecosystem:
- Regular Updates: Keep firmware and software up to date to patch vulnerabilities and ensure your devices are protected against the latest threats.
- Strong Passwords: Use strong, unique passwords for all devices and accounts to prevent unauthorized access.
- Network Segmentation: Isolate IoT devices from critical systems by segmenting your network, reducing the risk of widespread attacks.
- Monitoring: Continuously monitor network traffic for suspicious activity, enabling swift action to mitigate potential threats.
Common Challenges in IoT Security
Despite the availability of advanced security solutions, securing IoT devices remains a complex task. Some of the common challenges include:
Limited Resources
Many IoT devices have limited processing power and memory, making it challenging to implement complex security protocols. This requires careful consideration when selecting tools and solutions.
Interoperability Issues
Devices from different manufacturers may not be fully compatible, leading to potential security gaps. Ensuring interoperability and standardization is crucial for maintaining a secure IoT ecosystem.
The Future of IoT and P2P SSH
As technology continues to advance, the future of IoT and P2P SSH looks promising. Innovations in quantum computing, blockchain, and artificial intelligence are expected to revolutionize IoT security. These advancements will enable more secure and efficient communication between devices, paving the way for a safer and more connected world.
Comparing Popular SSH Tools
To help you choose the right tool for securing IoT P2P SSH connections, here's a comparison of some popular SSH tools:
| Tool | Platform | Features | Price |
|---|---|---|---|
| OpenSSH | Linux, macOS, Windows | Full SSH protocol support | Free |
| Dropbear | Embedded systems | Lightweight SSH server | Free |
| Bitvise | Windows | Advanced tunneling options | Free for personal use |
Conclusion
In conclusion, securing remote IoT P2P SSH connections is essential for protecting your devices and data in an increasingly connected world. By understanding the basics of SSH, utilizing free tools, and following best practices, you can significantly enhance the security of your IoT ecosystem. Staying informed about the latest developments in IoT security and adapting your strategies accordingly is key to ensuring long-term protection.
We encourage you to share your thoughts and experiences in the comments below. Additionally, feel free to explore other articles on our site for more insights into technology and security. Together, let's build a safer digital future!
Article Recommendations